Cyberwal in Galaxia
2024 Cyberwal in Galaxia Program
This school is free of charge* (registration below)
02 – 06 December 2024 (end of registrations on 25/11)
This program will take place on the Galaxia site in Transinne which, together with the European Space Agency (ESA) and the ESEC Centre in Redu (5 km away), forms a leading Space center in Europe.
Together for Cybersecurity - Investing in cybersecurity for a secure future -
Together for Cybersecurity - Investing in cybersecurity for a secure future -
The first International School linked to the Cyberwal initiative welcomes its third cohort with more than 200 European participants expected, this December 2nd, in the province of Luxembourg.
To address cybersecurity challenges and cybercrime threats, Wallonia has launched a cybersecurity policy named “Cyberwal by Digital Wallonia.” This initiative, part of the Walloon Recovery Plan, supports specific actions including research, innovation, and education within an “excellence hub”.
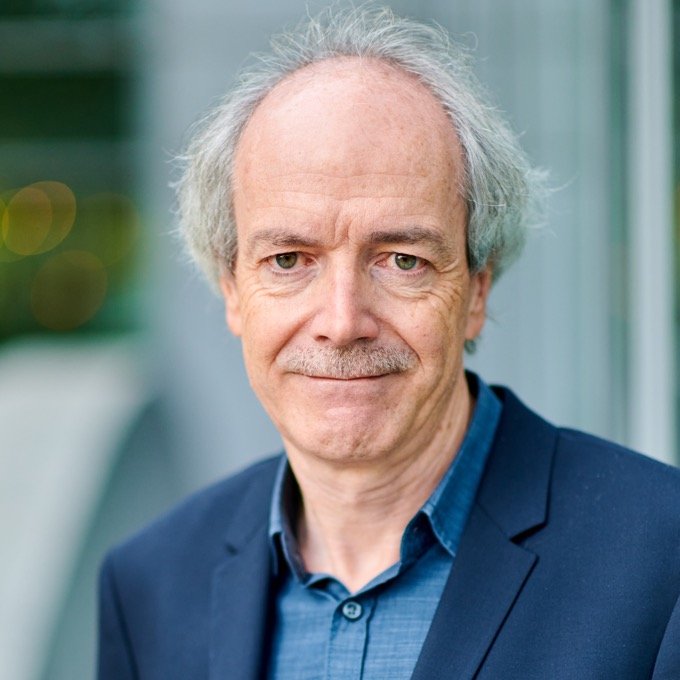
This school is the result of the ambition and determination of IDELUX and its partners. The goal is to develop a high-level international training center over the long term, under the authority of a scientific committee chaired by Mr. Axel LEGAY, Professor of Cybersecurity at UCLouvain, in response to the needs of institutions (such as ESA), businesses, public authorities, and more broadly, civil society.

The Cyberwal initiative positions the Wallonia Region as one of the key players in Belgian regional cybersecurity policy. It is notable that the vision of IDELUX and its partners is quickly becoming a reality, evolving quickly to meet current and future cybersecurity challenges at both national and transnational levels.
The goal is indeed to rapidly elevate Wallonia to a position of global excellence in cybersecurity and to ensure future editions of the “Cyberwal in Galaxia Program” achieve a European dimension of excellence by directly linking them with the ever-evolving needs of the international cyber ecosystem.

It is in the ESEC Centre in Redu that ESA has decided to base its cybersecurity center, which will ensure the cyber protection of the Agency’s ground and airborne activities.

Cyberwal in Galaxia
Speakers
The objective of the organizers is to position these courses as a high level of education, on a European scale, and to link them directly to the needs of the cyber ecosystem.
Cyberwal in Galaxia
Key speakers
The objective of the organizers is to position these courses as a high level of education, on a European scale, and to link them directly to the needs of the cyber ecosystem.

Kim Guldstrand Larsen
Cyberwal in Galaxia
Speakers

Maxime Cordy
President of the Scientific Committee

Axel Legay
Our Program for the 5 days
The program includes theoretical & practical courses.
A break is scheduled every day in the morning and afternoon.
The next editions of Cyberwal in Galaxia Program are already planned for 2025.
- Day 1
Monday 02/12
- Day 2
Tuesday 03/12
- Day 3
Wednesday 04/12
- Day 4
Thursday 05/12
- Day 5
Friday 06/12
Sold out
AI and Cybersecurity day 2024
The rise of artificial intelligence (AI) is having a profound impact on our society. During 2024, AI continues to be rapidly integrated into various sectors, each leveraging the technology to improve efficiency, reduce costs, and provide better services. The use of AI has expanded across industries, but some sectors have seen particularly high levels of adoption and integration such as healthcare (diagnostics, drug discovery, personalized medicine, predictive analytics), finance and banking (fraud detection, algorithmic trading, credit scoring, customer service), retail and e-commerce (personalized recommendations, inventory Management, customer service, pricing optimization), manufacturing and industry 4.0 (predictive maintenance, quality control, supply chain optimization, robotics and automation), automotive and transportation (autonomous vehicles, driver assistance systems, logistics and fleet management, predictive maintenance), energy and utilities (Smart Grid management, predictive maintenance, energy consumption optimization, renewable energy management), telecommunications (network optimization, predictive maintenance, customer support, fraud detection) and education (personalized learning, automated Grading, tutoring systems, administrative efficiency). AI is having impact and driving innovation by providing improved efficiency, increased productivity, better decision-making, improved healthcare, or environmental sustainability.
AI research has advanced in 2024 with advancements in Large Language Models (more powerful models, fine-tuning and adaptability, reduced hallucinations), generative AI and multimodal models (image and text integration, video and audio generation, creative applications).
However as AI and machine learning systems become more prevalent and integral to various applications, they also become more attractive targets for cyberattacks. Some of the new and evolving cybersecurity threats to AI and machine learning in 2024 are adversarial attacks, data poisoning, model inference attacks, model evasion attacks, backdoors attacks, membership inference attacks, federated learning Attacks, supply chain attacks and cloud infrastructure attacks. Cybersecurity is important for AI because AI systems are increasingly being used in critical infrastructure, such as power grids and transportation systems. If these systems are hacked, it could have a devastating impact on society.
The objective of the day is to present some key research topics at the intersection of AI and cybersecurity in the form of short tutorials or research presentations. The day will address topics on how AI is being used for threat identification, protection, detection, response and recovery. More specific topics such as Explainable AI for malware analysis, AI based AI-powered anomaly detection, AI-powered malware detection and AI-powered incident response will also be addressed.
09:00 AM – 10:00 AM
REGISTRATIONS
10:00 AM – 10:05 AM
- Auditorium
Introduction
- AI in Cyber Security leverages the industrial cyber security power of machine learning and data analysis to augment traditional security measures.
- Zero Trust Architecture brings a new security level in OT/ICS environment.
- How can the Industrial Metaverse help to secure our Industry 4.0 ?

Philippe Massonet - Scientific Coordinator at CETIC

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

David Prada
10:05 AM – 11:00 AM
- Auditorium
Statistical Model Checking for Secure Cyber-Physical Systems
Cyber-physical or IoT systems are ubiquitous in modern society, and involve computational devices monitoring and controlling complex physical systems. The computational devices are often constrained by computational power, memory, and energy consumption, and are increasingly used in critical industrial systems. Clearly the safety and security of such systems is of the utmost importance. In this talk we will present a number of settings, where so-called Statistical Model Checking (SMC) — supported by the award-winning tool UPPAAL (www.uppaal.org) – has been used to identify and quantify potentially security side-channel attacks.
In order to formally specify security-related properties—such as non-interference—one cannot purely rely on traditional trace-based specification formalisms such as Linear Temporal Logic (LTL). The reason is that they relate the events of two (or more) traces of the system, and LTL can only reason on one execution at a time. So-called hyper-property extensions of LTL has been proposed. Within UPPAAL a real-time and probabilistic hyper-logic (HPSLT) has been implemented and used to identify three types of side-channel attacks.
DTLS is a protocol that is widely used by IoT devices, including critical industrial IoT systems, as the transport layer for secure and authenticated communication. A formal model of DTLS has been made, and the statistical model checking engine of UPPAAL has been used to analyse, evaluate, and optimise energy consumption for the protocol. In particular different network scenarios has been considered identifying how energy consumption is highly dependent on the specific usage scenario. Addressing security issues the model has been extended with an active attacker trying to drain as much energy as possible from the target system by (ab)using DTLS. Analysing and preventing such Denial of Service attacks is essential for critical systems.
Finally, we will report on use of the statistical model checking engine of UPPAAL for analysing impact of bit-flips in security critical code.

Kim Guldstrand Larsen - Professor at Aalborg University, Department of Computer Science, Denmark

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

David Prada
11:00 AM – 11:45 AM
- Auditorium
Machine Learning Security in the Real World
Adversarial attacks are considered as one of the most critical security threats for Machine Learning (ML). In order to enable the secure deployment of ML models in the real world, it is essential to properly assess their robustness to adversarial attacks and develop means to make models more robust. Traditional adversarial attacks were mostly designed for image recognition and assume that every image pixel can be modified independently to its full range of values.
In many domains, however, these attacks fail to consider that only specific perturbations could occur in practice due to the hard domain constraints that delimit the set of valid inputs. Because of this, they almost-always produce examples that are not feasible (i.e. could not exist in the real world). As a result, research has developed real-world adversarial attacks that either manipulate real objects through a series of problem-space transformations (i.e. problem-space attacks) or generate feature perturbations that satisfy predefined domain constraints (i.e. constrained feature space attacks). In this talk, we will review the scientific literature on these attacks and report on our experience in applying them to real-world cases.

Maxime Cordy - Research Scientist at the Interdisciplinary Center for Security, Reliability and Trust (SnT)

Laurens Singier - Cybersecurity IT/OT researcher , Ethical hacker
11:45 AM – 12:00 PM
COFFEE BREAK
12:00 PM – 01:00 PM
- Auditorium
Turing's Echo on Deceptive Machines: The Challenge of Distinguishing Human and AI Creations
As generative AI models evolve, distinguishing between human-generated and AI-generated content is becoming increasingly challenging, threatening trust across various domains such as misinformation in media, political campaigns, legal accountability, scientific integrity, and cybersecurity. Distinguishing between machine and human outputs will be vital because, in the dystopian future, machines will potentially rise against humans.
This talk explores methods and technologies for identifying the origin of content, focusing on audio and text. We highlight the limitations of current models in detecting subtle differences between human-generated and AI-generated content. Our work augments physical principles, such as the Micro Doppler Effect, with machine learning frameworks. This integration incorporates prior input data knowledge into the model, enhancing detection and reducing biases in generated content. Finally, we discuss ongoing challenges and future research directions in this dynamic field.

Ahmad-Reza Sadeghi - Professor Dr.-Ing. at technische universität darmstadt

Laurens Singier - Cybersecurity IT/OT researcher , Ethical hacker
01:00 PM – 02:00 PM
LUNCH TIME
02:00 PM – 03:30 PM
- Auditorium
Explainable ML for malware analysis
The talk addresses the growing complexity of malware by exploring advanced detection and analysis techniques, focusing on both static and dynamic approaches. The lecture highlights the strengths and limitations of each approach and discusses their combination to improve detection accuracy. A method of representing malware as images is introduced, allowing the application of image processing and machine learning techniques to detect malicious patterns, offering advantages over traditional methods. The importance of explainability in malware detection is advocated by using such approaches.

Fabio Martinelli - Research Director at National Research Council of Italy

Laurens Singier - Cybersecurity IT/OT researcher , Ethical hacker
03:30 PM – 03:45 PM
COFFEE BREAK
03:45 PM – 04:30 PM
- Auditorium
Cybersecurity threat landscape, Microsoft's view on the current and future secure state
During this session, Microsoft will show their view on the threat landscape and how is has evolved throughout the years using geopolitical challenges, technical advancements by integrating cutting-edge technologies into their attacks and how we should prepare, defend and collaborate as one to become more resilient and secure in this ever-changing world

Bart Asnot - National Security Officer at Microsoft

Laurens Singier - Cybersecurity IT/OT researcher , Ethical hacker
04:30 PM – 05:15 PM
- Auditorium
Artificial Intelligence Deployable Agent (AIDA)
Contemporary combat systems carry an increasing amount of tactical computing and electronics potentially vulnerable to cyber-attacks. While current cyber-defense operations address in non-real time the needs for detection and response to cyber incidents affecting traditional IT systems, securing the fast expanding Internet of Military Things (IoMT) requires very short response times, and accurate decision making under strong operational, computing and energy constraints. The deployment of efficient detection and response capacities on embedded systems requires the design of lightweight resident Artificial Intelligence (AI) agents, trained specifically for these environments and capable of automating the detection and response loop in the absence of timely available human expertise. NATO’s IST-152 Research Task Group (2016-2020) on “Intelligent, Autonomous and Trusted Agents for Cyber Defense and Resilience” (AICA) initiated this concept between 2016 and 2020. The research yielded an AICA Reference Architecture (Kott et al., 2018). Later, an international working group formed to continue work on AICA (see https://www.aica-iwg.org/). Yet this highly conceptual architecture was not yet set into practice. The growing use of Unmanned Vehicles (UxV) in modern conflicts however revives the need for time sensitive autonomous decision at the edge of systems evolving in environments saturated with Cyber-Electromagnetic Threats (CEMA). To reduce UxVs exposure and augment their chances of survival in contested battlefield, remote control is progressively replaced by individual (autonomous) and collective (swarm) intelligent navigation techniques. While AI is seen as an essential capability for the survival of these proliferating objects, adversarial AI discipline unveils targeted evasion techniques to lure and hide from embedded AI. In short we need cyber-defense agents that are altogether frugal, accurate, adaptive, explainable, collaborative, and robust. This is the challenge addressed by AIDA project.
The proposed solution relies on three types of AI agents: a white agent, a red agent, and a blue agent. The white agent is a foundation model that is trained against massive data to develop a broad set of human-like capacities such as threat analysis, detection rule edition, incident qualification and response planning. Cyber-defense analysts prompt a Large Language Model (LLM) upon identification of new threats to produce tailored detection rules and response plans in seconds instead of hours. A Retrieval Augmented Generation (RAG) procedure restricts LLM sources to qualified knowledge bases. A reward system based on human feedback reinforces the model toward good decisions. From this white agent, smaller, more specialized agents will be derived that aim to perform narrow cyber-defense routines at the edge of IoMT. Unlike the white agent, blue agents need to operate in resource-constrained environment in an autonomous manner. We will use pruning and unlearning techniques to minimize the resource requirements of blue agents and obfuscation techniques to reduce their exposure to reverse engineering. Wherever needed, they will be fine-tuned to their environment of destination across land, sea, air, space and cyber domains. Yet as we may lack quantitative attack data, we will craft a third type of agent, whose role will be to generate attacks. The red agent will be trained in a simulated environment placed in adversarial setup with blue agents to develop offensive AI strategies. This Generative Adversarial Networks (GAN) setup will reinforce blue agents’ successful defense strategies, challenge their individual and collaborative defense objectives, and strengthen their robustness towards evasion attacks.
To conclude, the AIDA system involves an LLM (white agent), adversarial generative AI (red agent) and a Multi-Agent System (blue agents) in mission-critical activities landing in 5 military domains. Among other applications, the system aims to protect combat aircraft against CEMA threats with severe safety implications. Continuous improvement and responsible use of AI are enabled by reinforcement learning and RAG techniques. It reduces the exposure of modern military systems to emerging risks such as adversarial AI attacks.

Adrien Becue - AI & Cybersecurity Expert at THALES

Laurens Singier - Cybersecurity IT/OT researcher , Ethical hacker
05:15 PM – 05:30 PM
- Auditorium
Kick-off SecuWeb: Towards a new and safer internet
SecuWeb aims to strengthen data security in companies and organisations in Flanders, Wallonia and France. The project investigates how innovative technologies such as Solid, Blockchain, Quantum Internet, 5G, AI and IoT can contribute to safer data use. Through demonstrators and use cases, we explore how to implement these technologies in companies and organisations. We focus on key sectors for our regions such as healthcare, industry 4.0, mobility and nutrition.
SecuWeb is an Interreg France-Wallonie-Vlaanderen project under the coordination of TUA West in cooperation with CITC, Eurasanté, Howest, Idelux, Sirris, UCLouvain, UGent and UPHF.

Marwane Ayaida - Professor at Université Polytechnique Hauts-de-France

Emmelie Houzet - project leader at TUA West
Sold out
Quantum Day
08:30 AM – 09:00 AM
REGISTRATIONS
09:00 AM – 10:30 AM
- Auditorium
Cybersecurity in our quantum age
Although practised as an art and science for ages, cryptography had to wait until the mid-twentieth century for Claude Shannon to endow it with a rigorous mathematical foundation. However, Shannon’s approach was rooted in his own information theory, itself inspired by the classical physics of Newton and Einstein. Yet, the world in which we live is subject to the laws of quantum theory, no matter how bewildering, whose experimental verification half a century ago was rewarded in 2022 by the Nobel Prize in Physics. When quantum theory is taken into account, new vistas open up both for codemakers and codebreakers. Is this a blessing or a curse for cybersecurity? Quantum computers will soon be capable of computations that would be unthinkable for a conventional computer, which will seriously undermine the so-called security of Internet communications as we practise them today. Nevertheless, the same quantum theory gives rise to new cryptographic paradigms that are in principle invulnerable to arbitrary attacks, even by an adversary capable of harnessing unlimited computing power and technology. However, this unconditional security requires quantum cryptography to be implemented according to the theory, which is very challenging. Will the cat-and-mouse game between codebreakers and codemakers soon reach a decisive outcome? As we shall see, the jury is still out!
No prior knowledge in cryptography or quantum theory will be assumed. Please note that this talk will be given in French, with slides written in English.

Gilles Brassard - Professor of Montreal University
10:30 AM – 10:45 AM
COFFEE BREAK
10:45 AM – 12:15 PM
- Auditorium
Cybersecurity in our quantum age
Although practised as an art and science for ages, cryptography had to wait until the mid-twentieth century for Claude Shannon to endow it with a rigorous mathematical foundation. However, Shannon’s approach was rooted in his own information theory, itself inspired by the classical physics of Newton and Einstein. Yet, the world in which we live is subject to the laws of quantum theory, no matter how bewildering, whose experimental verification half a century ago was rewarded in 2022 by the Nobel Prize in Physics. When quantum theory is taken into account, new vistas open up both for codemakers and codebreakers. Is this a blessing or a curse for cybersecurity? Quantum computers will soon be capable of computations that would be unthinkable for a conventional computer, which will seriously undermine the so-called security of Internet communications as we practise them today. Nevertheless, the same quantum theory gives rise to new cryptographic paradigms that are in principle invulnerable to arbitrary attacks, even by an adversary capable of harnessing unlimited computing power and technology. However, this unconditional security requires quantum cryptography to be implemented according to the theory, which is very challenging. Will the cat-and-mouse game between codebreakers and codemakers soon reach a decisive outcome? As we shall see, the jury is still out!
No prior knowledge in cryptography or quantum theory will be assumed. Please note that this talk will be given in French, with slides written in English.

Gilles Brassard - Professor of Montreal University
12:15 PM – 01:15 PM
LUNCH TIME
01:15 PM – 02:00 PM
- Auditorium
BeQCI and device-independent quantum key distribution
This presentation provides a brief introduction to the Belgian Quantum Communication Infrastructure (BeQCI) project, part of the European EuroQCI initiative aimed at advancing secure quantum communication networks across Europe. In addition to building infrastructure, BeQCI is driving research into future-proof quantum key distribution (QKD) protocols. Specifically, we will explore Device-Independent (DI) QKD, a cutting-edge approach to quantum cryptography that leverages Bell inequalities, recognized with the 2022 Nobel Prize in Physics. By eliminating certain security assumptions, DI QKD offers unprecedented levels of security beyond current QKD protocols. Attendees will gain insights into the future potential of DI and semi-DI QKD to enhance information security in the quantum era. Join us to discover how these advancements are pushing the boundaries of secure communication.

Prof. Stefano Pironio - FRS-FNRS Research Director at ULB
02:00 PM – 02:45 PM
- Auditorium
Eagle-1 : QKD in practice and build-up of users communities
The EAGLE-1 mission aims to develop Europe’s first sovereign, end-to-end space-based Quantum Key Distribution (QKD) system. Led by SES in collaboration with the European Space Agency (ESA) and various European space agencies and private partners, the mission will feature a state-of-the-art QKD system comprising a payload aboard the EAGLE-1 Low Earth Orbit (LEO) satellite, optical ground stations, quantum operational networks, and a key management system. EAGLE-1 marks a significant milestone in next-generation quantum communication infrastructure, providing crucial technical insights and mission data while contributing to the EuroQCI program‘s development. It offers a unique opportunity for public and private entities to test and validate end-to-end Quantum Safe solutions through satellite-based QKD.

Thierry Draus - Vice President Business Development at SES
02:45 PM – 03:30 PM
- Auditorium
Quantum Technologies for Communications Systems
In this talk, we will explore the exciting advancements in quantum technologies and their transformative impact on communication systems. Starting with an introduction to the Second Quantum Revolution, we will delve into key developments, such as Quantum Communications Infrastructure and Quantum Key Distribution (QKD), which are poised to enhance data security and revolutionize the way we exchange information. Next, we will discuss the concept of the Quantum Internet, a futuristic network leveraging quantum principles for unprecedented communication capabilities. We will also cover Quantum Optimization techniques and their application to solving complex communication challenges, especially within large-scale and evolving networks like 6G. Finally, we will conclude with prespectives and open research problems offering a roadmap for the development and integration of quantum technologies in the years ahead.

Seid Koudia - Research Associate at University of Luxembourg
03:30 PM – 04:15 PM
- Auditorium
Fast and Practical integrated quantum communications systems
FranceQCI and its challenges
We discuss current efforts towards the deployment of a national quantum communication infrastructure in France. These include technologies under development in our academic laboratories as well as benchmark demonstrations at the testbeds in operation in the Paris and Nice regions involving industrial actors spanning the telecom operator, cybersecurity, QKD system provider, photonics and space sectors. We also discuss current challenges in the field of quantum communication and future perspectives.

Professor Eleni Diamanti - CNRS Research Director at Sorbonne University
Prof. Hugo Zbinden - University of Geneva
04:15 PM – 04:30 PM
COFFEE BREAK
04:30 PM – 05:15 PM
- Auditorium
INT-UQKD : cross-border QKD
Through a set of business-driven use cases, INT-UQKD (“International Use cases for Operational QKD Applications & Services”) will provide global quantum safe communication services upon a hybrid space-terrestrial quantum key distribution (QKD) backbone. By leveraging the QKD technology, together with other classical and post-quantum cryptographic protocols to deliver a practical environment that can be used in the current commercial context, INT-UQKD safeguards the secure exchange of information, the long-term protection of stored data, and the protection of critical infrastructure in the post quantum age.
Thanks to its hybrid space and terrestrial network, INT-UQKD will demonstrate a global quantum safe communication between Redu (Belgium), Windhof (Luxembourg) and Singapore. As INT-UQKD architecture is designed with scalability and interoperability mind, it allows the incorporation of future extensions. These extensions will expend both INT-UQKD geographical reach and operational capabilities, aiming at implementing a resilient, flexible and manageable ecosystem with global coverage enabling quantum secure communication and cryptographic services for private and governmental users.

Patrick Renaux - Senior cybersecurity architect
05:15 PM – 06:15 PM
- Visit
Presentation of Quantum Demonstrator of GALAXIA in Transinne (Thales Belgium)
Presentation of Quantum Demonstrator of GALAXIA in Transinne (Thales Belgium)

Jonathan Pisane - Innovation & Product Policy Manager at Thales Belgium
9:00 AM – 9:30 AM
REGISTRATIONS
09:30 AM – 12:30 PM
- Auditorium
Poster session (Abstract)
The 3rd edition of the Cyberwal in Galaxia Program will feature an exciting poster competition where 30 posters will be showcased. The best poster will be honored with an Award, which will be presented during the ceremony scheduled for Wednesday, 12/04, in the late morning. An expert jury, consisting of 10 professionals renowned in their fields, will select the winner of this Cybersecurity Award.
Beyond the competition, the poster session offers an exceptional opportunity for participants to present their innovative research and hone their scientific communication skills in front of a diverse audience, including business representatives. This session is much more than a mere contest: it is a true exchange platform. It enables participants to connect, share ideas, and enrich the international cybersecurity community.
We warmly invite students, researchers, and professionals to participate in this enriching event. Discover the latest innovations, share your expertise, and immerse yourself in an environment of collaboration and innovation. Join us to celebrate excellence in cybersecurity and contribute to a tradition of impact and continuous progress.
09:30 AM – 09:45 AM
Introduction of the poster session (overview, objectives, connecting of researchers with industries)
Poster session
Presentation of CyberActive
CyberActive offers free training, videos and learning resources to increase the cyber resilience of the manufacturing and digital services (SaaS) sectors. The subjects covered cover the main challenges facing these companies, for different types of profiles within the organisations.
This project is led by cybersecurity experts from Sirris, Howest, UCLouvain and VUB, and is funded by the FPS Economy and the European Commission.
Discover our offer on www.cyberactive.be.

Thierry Coutelier - Senior Expert at Sirris
Awarding of the Best Poster & presentation by the winner
End
12:30 PM – 01:30 PM
LUNCH TIME
01:30 PM – 03:00 PM
- Auditorium & ISS
Introduction
A meticulously designed CTF challenge that push the boundaries of conventional cybersecurity knowledge. Attendees will be able to revel in the opportunity to listen to and interact with esteemed experts from the cybersecurity domain, each bringing a wealth of experience and fresh perspectives.
Complementing these, our hands-on demonstrations promise a deep dive into the latest technologies and methodologies, forging a link between academic theories and their tangible, real-world implementations. Join us for a comprehensive exploration of the future of cybersecurity.
Deloitte will invite keynotes speakers to develop on concise and insightful talk on a relevant cybersecurity topic and allow some time for questions and answers.

Nicolas Noël - Director, Cyber Risk Advisory at Deloitte

Etienne Caron - Manager, Cyber Risk Advisory at Deloitte
03:00 PM – 03:15 PM
coffee break
03:15 PM – 04:45 PM
- Auditorium & ISS
A meticulously designed CTF challenge that push the boundaries of conventional cybersecurity knowledge. Attendees will be able to revel in the opportunity to listen to and interact with esteemed experts from the cybersecurity domain, each bringing a wealth of experience and fresh perspectives.
Complementing these, our hands-on demonstrations promise a deep dive into the latest technologies and methodologies, forging a link between academic theories and their tangible, real-world implementations. Join us for a comprehensive exploration of the future of cybersecurity.
Deloitte will invite keynotes speakers to develop on concise and insightful talk on a relevant cybersecurity topic and allow some time for questions and answers.

Nicolas Noël - Director, Cyber Risk Advisory at Deloitte

Etienne Caron - Manager, Cyber Risk Advisory at Deloitte
08:30 AM – 09:00 AM
REGISTRATIONS
09:00 AM – 12:15 PM
- ISS
An Introduction to Smart Contracts Security
This session focus on security aspect of modern financial transactions above blockchains: smart contracts. To do so, the first part of the session will review key theoretical concepts, such as cryptography, hashing, signature, fingerprint, merkle tree) before diving into the notion of block chain and smart contracts. The Solidity programming language will be introduced and well known attacks will be discussed (e.g., reentrancy attack). In the second part of the session, attendees will have the opportunity to learn how to detect security breaches in smart contracts and how to abuse them for performing an attack.

Benoît Donnet - Professeur at Université de Liège
OR
09:00 AM – 09:45 AM
- Auditorium
The blockchain landscape in Wallonia
Wallonia is active in the field of blockchain, and a number of public and private initiatives are already underway. Before presenting some concrete projects implemented in our region, Nicolas Point will outline the two most important federative programs.
The WalChain initiative, which was born of a grouping of Walloon blockchain start-ups, aims to promote ‘Made In Wallonia’ blockchain as an innovative tool for building collaborative and transparent ecosystems, as well as an opportunity to contribute to sustainable economic redeployment in Wallonia. DigitalWallonia4.Trust is an innovative project led by Agoria, Infopole, Agence du Numérique and WalChain. Supported by the Service Public de Wallonie Economie Emploi et Recherche (SPW EER) and Wallonia, this initiative is part of the Digital Excellence program of Wallonia’s digital strategy, Digital Wallonia. DW4TRUST aims to place Wallonia at the center of digital innovation. By integrating blockchain technology into various sectors, DW4TRUST not only improves efficiency, trust and security across businesses, but also opens up new opportunities for growth and innovation.

Nicolas Point - Responsable du département IT at MULTITEL

Aloïs Moubax - Program Manager at DigitalWallonia4.Trust
09:45 AM – 10:30 AM
- Auditorium
Seamless Blockchain Integration: Transforming Existing Businesses with Innovative Solutions
This session will explore a proven methodology for integrating blockchain technology into existing business systems. We’ll cover key steps, from assessing business needs and designing a tailored blockchain strategy, to implementing and deploying solutions that align with current infrastructure. Attendees will learn best practices for overcoming common challenges, such as data migration, interoperability, and security, while maximizing the benefits of blockchain, including transparency, efficiency, and trust. Real-world case studies will highlight successful integrations in sectors like supply chain, ESG reporting, and Digital Product Passports (DPP).

Harold Kinet - CEO at BE Blockchain
10:30 AM – 10:45 AM
COFFEE BREAK
10:45 AM – 11:45 AM
- Auditorium
Logion: Blockchain and IPFS to Secure and Certify Sensitive Data
In a world where digital threats are rapidly evolving, the need for advanced solutions to secure sensitive data is paramount. Logion offers an innovative approach by combining blockchain technology with IPFS (InterPlanetary File System). This combination not only ensures the integrity and traceability of data but also guarantees its availability and immutability. Blockchain, with its decentralized nature, provides an unalterable and transparent ledger, while IPFS enables distributed and resilient file storage. Together, these technologies offer a robust alternative to traditional storage solutions, meeting the increasing demands for security in cyberspace. This session will explore how Logion leverages these technologies to provide superior protection for sensitive data, particularly in sectors where confidentiality and security are crucial. Participants will learn how the combination of blockchain and IPFS can not only enhance data security but also facilitate certification and traceability, all while adhering to the strictest privacy standards.

David Schmitz - Founder of Logion

Gérard Dethier - CTO at Logion
11:45 AM – 12:15 PM
- Auditorium
The Future of Blockchain and Web3 in Wallonia
In a world where digital threats are rapidly evolving, the need for advanced solutions to secure sensitive data is paramount. Logion offers an innovative approach by combining blockchain technology with IPFS (InterPlanetary File System). This combination not only ensures the integrity and traceability of data but also guarantees its availability and immutability. Blockchain, with its decentralized nature, provides an unalterable and transparent ledger, while IPFS enables distributed and resilient file storage. Together, these technologies offer a robust alternative to traditional storage solutions, meeting the increasing demands for security in cyberspace. This session will explore how Logion leverages these technologies to provide superior protection for sensitive data, particularly in sectors where confidentiality and security are crucial. Participants will learn how the combination of blockchain and IPFS can not only enhance data security but also facilitate certification and traceability, all while adhering to the strictest privacy standards.

Moderator: Aloïs Moubax - Program Manager at DigitalWallonia4.Trust

Moderator: Nicolas Point - Head of the IT Department

David Schmitz - Founder of Logion

Gérard Dethier - CTO at Logion

Harold Kinet - CEO at BE Blockchain
12:15 PM – 01:15 PM
LUNCH TIME
01:15 PM – 04:15 PM
- ISS
An Introduction to Smart Contracts Security
This session focus on security aspect of modern financial transactions above blockchains: smart contracts. To do so, the first part of the session will review key theoretical concepts, such as cryptography, hashing, signature, fingerprint, merkle tree) before diving into the notion of block chain and smart contracts. The Solidity programming language will be introduced and well known attacks will be discussed (e.g., reentrancy attack). In the second part of the session, attendees will have the opportunity to learn how to detect security breaches in smart contracts and how to abuse them for performing an attack.

Benoît Donnet - Professeur at Université de Liège
OR
01:15 PM – 02:30 PM
- Auditorium
Emerging ICT trends: the need for secure and quantum-safe networks
We will highlight the increasing need to have strong network security resulting from the adoption of new technologies like AI, 5G, IoT and quantum. We will review the different network security technologies available on offer today. And we will explore the impact of crypto-relevant quantum computers on organisations, and how you can already prepare today.

Wim Van Vossel - Technology Strategy & Innovation Manager

Kristof Spriet - Product Owner Smart & Secure Networks
02:30 PM – 03:30 PM
- Auditorium
AI-enabled disconnected sovereign cloud in Luxembourg for Europe
Clarence’s core mission is to offer a cutting-edge, disconnected sovereign cloud solution. Based on Google Cloud technology, this unique proposition guarantees the confidentiality and security of the most sensitive information, giving control over data, and offering total autonomy of operation. Clarence respects the highest ethical standards in data protection, confidentiality, transparency and regulatory compliance.
Clarence is the result of a joint venture between Proximus and LuxConnect. A joint venture born of the desire to create a disconnected sovereign cloud, designed to meet the needs of companies wishing to retain control over the integrity of their data and access to it, but also, operationally, to ensure that their operations are carried out on our soil and subject only to European jurisdictions.
The origins of Clarence lie in a shared ambition: to offer users the most advanced Cloud functionalities, while guaranteeing them total control over where their data resides and who has access to it.
What We Do : Combining Innovation and Sovereignty in Cloud Computing
The sovereign cloud solves the dilemma between innovation and compliance. By combining the best of both worlds, it facilitates access to technological innovations while ensuring compliance and protection of sensitive data.

Moderator: Jean-François Terminaux - Head of Product Management - Disconnected Cloud at Proximus
03:30 PM – 03:45 PM
COFFEE BREAK
03:45 PM – 04:45 PM
- Auditorium
Cloud Continuum Security Challenges
EU IPCEI on Next Generation Cloud Infrastructure and Services
Cloud & edge computing are crucial for an interconnected and resilient Digital Europe, as well as for the EU’s geostrategic position and competitiveness in the global economy. IPCEI CIS is the first IPCEI in the cloud and edge computing domain. It concerns the development of the first interoperable and openly accessible European data processing ecosystem, the multi-provider cloud to edge continuum. It will develop data processing capabilities, and software and data sharing tools that enable federated, energy-efficient and trustworthy cloud and edge distributed data processing technologies and related services. The innovation provided by IPCEI CIS will enable a new spectrum of possibilities for European businesses and citizens, advancing the Digital and Green transition in Europe.The main aim of the session is to introduce the main cloud continuum security challenges focusing on relevant topics like Confidential Computing, ultra-high resilience, cloud certification, etc.

Jordi Guijarro - Principal Technologist at Cloud-Edge Innovation
04:45 PM – 05:30 PM
- Auditorium
A Tale of Vulnerability Prediction
Over the past years, automated vulnerability prediction research, mainly supported by AI techniques, has grown in popularity. While a large number of studies have been proposed, they often make simplification assumptions, which limit their applicability and adoption. This talk will provide a historical view of the vulnerability prediction approaches and will focus on the challenges and limitation that they face through the lens of three different research communities, i.e., AI, SE and Security. The talk will conclude with a discussion on the links between vulnerability prediction and testing, showing potential applications and cross-fertilization between the two research fields.

Mike Papadakis - Associate Professor at SnT
05:30 PM – 06:00 PM
- Auditorium
How sovereign cloud solutions contribute to European digital autonomy?
Round table on Blockchain in Wallonia
In a world where digital threats are rapidly evolving, the need for advanced solutions to secure sensitive data is paramount. Logion offers an innovative approach by combining blockchain technology with IPFS (InterPlanetary File System). This combination not only ensures the integrity and traceability of data but also guarantees its availability and immutability. Blockchain, with its decentralized nature, provides an unalterable and transparent ledger, while IPFS enables distributed and resilient file storage. Together, these technologies offer a robust alternative to traditional storage solutions, meeting the increasing demands for security in cyberspace. This session will explore how Logion leverages these technologies to provide superior protection for sensitive data, particularly in sectors where confidentiality and security are crucial. Participants will learn how the combination of blockchain and IPFS can not only enhance data security but also facilitate certification and traceability, all while adhering to the strictest privacy standards.

Moderator: Jean-François Terminaux - Head of Product Management - Disconnected Cloud at Proximus

Wim Van Vossel - Technology Strategy & Innovation Manager

Jordi Guijarro - Principal Technologist at Cloud-Edge Innovation

Mike Papadakis - Associate Professor at SnT
Sold out
06:00 PM – 07:00 PM
- Hub
Aperitif
07:30 PM
- Voyager café
Gala Dinner at the Euro Space Center
08:30 AM – 09:00 AM
REGISTRATIONS
09:00 AM – 10:00 AM
- Auditorium
Innovation and judicial police: a winning combination in the fight against crime
The Federal Judicial Police will present its overall vision and the role of technology in achieving it.
The main drivers of our strategy will be outlined to explain their use in our digital transformation and the disruption of our operational processes.
We will provide concrete examples of technological achievements in operations where an inclusive approach has been a key factor in success.
We will then discuss the challenges of operational Big Data and the contribution of AI to our complex processes.

David JAROSZEWSKI - Senior advisor on digital transformation and innovation
10:00 AM – 10:45 AM
- Auditorium
Introduction – The hack of the city of Antwerp and lessons learned (Amphi)
After a brief introduction to the current ransomware landscape, we review the case of the City of Antwerp based on information that was published by the city and in the press over the course of the attack and the months that followed – looking at the IT, operational, communication, reputation and financial impacts of the attack. The presentation is organized as a timeline of events, supported with press clippings and public facts brought ttogether into an exciting story that unravels over time

Didier Stevens - Senior Analyst at NVISO

Vincent Defrenne - Partner, Cyber Strategy & Architecture at NVISO
10:45 AM – 11:00 AM
coffee break
11:00 AM – 01:00 PM
- Auditorium & ISS
Crisis response exercise: the enemy from within (2 rooms)
Participants take the helm of the crisis management team of a fictitious energy producer running its operations across Eastern Europe, and are confronted with a rapidly evolving incident involving the compromission of some of their systems and the potential involvement of an internal system administrator in these activities. The exercise is organized as a succession of briefings from the incident response team and analysis in group to define together a course of action that responds to the events and the questions raised. The response of course consists of technical actions to analyse, isolate, contain and eradicate the threat, but also involves organizational measures and measures in terms of internal and external communication. The exercise is facilitated by seasoned crisis and incident responders Vincent Defrenne and Didier Stevens.

Didier Stevens - Senior Analyst at NVISO

Vincent Defrenne - Partner, Cyber Strategy & Architecture at NVISO
01:00 PM – 02:00 PM
LUNCH TIME
02:00 PM – 05:00 PM
- Auditorium & ISS
Ransomware Workshop (2 rooms)
During the workshop, participants will learn how to deal with this situation step-by-step by challenging them in their knowledge of various infosecurity topics. The goal of this workshop is to provide the participants with a structured approach on how to spot malware and how to deal with incidents caused by modern adversaries. Instructors will be assisting the students towards the full mapping of the incident and will provide a typical solution at the end of the workshop. The situation that the students will have to handle is as follows: “You are part of your company’s Incident Response team. On some idle Friday afternoon, your manager barges in. He has just been notified by the authorities that they have compromised a Commandand-Control server and that they have found systems communicating to that server originating from your company. The board of directors is breathing down his neck to find out what has happened and has asked him to contain this problem as soon as possible. How come we haven’t noticed this? What systems have been compromised? What data is exfiltrated?
Are there still active connections? You immediately coordinate with the authorities and receive an extract of the information they have pulled from the compromised server. And so you quest begins…” The students will work in teams of 2 and will have 4 hours to find out what has happened and to verify if there is still any active connections. During the workshop, the instructors will switch between guiding the participants and challenging them by assuming various positions in the company. The workshop will start with the set up of the participants machines with the tools required. For those participants that may not install such tools on their machine, a Linux-based virtual machine will be available for download or on USB sticks.

Didier Stevens - Senior Analyst at NVISO

Vincent Defrenne - Partner, Cyber Strategy & Architecture at NVISO
05:00 PM – 05:10 PM
- Auditorium
Closing words from Cyberwal in Galaxia team
05:00 PM
- Auditorium
The end
The next editions of Cyberwal in Galaxia Program are already planned for 2025.
Previous edition
2023 Cyberwal in Galaxia Program
04 – 08 December 2023
2022 Cyberwal in Galaxia Program
12 – 16 December 2022
Register now!