Cyberwal in Galaxia
2022 Cyberwal in Galaxia Program
This school is free of charge* (registration below) for the students enrolled at an university.
12 – 16 December 2022 (end of registrations on 05/12)
This program will take place on the Galaxia site in Transinne which, together with the European Space Agency (ESA) and the ESEC Centre in Redu (5 km away), forms a leading Space center in Europe.
Together for Cybersecurity - Investing in cybersecurity for a secure future -
Together for Cybersecurity - Investing in cybersecurity for a secure future -
Currently, the Galaxia Park hosts ESA’s educational activities, world-class companies specialized in Space and cybersecurity, and the Euro Space Center.

It is in the ESEC Centre in Redu that ESA has decided to base its cybersecurity center, which will ensure the cyber protection of the Agency’s ground and airborne activities.

The Euro Space Center is an educational center dedicated to space, which welcomes 15,000 young people per year, of 35 different nationalities, for 3 to 5 days of courses, as well as 70,000 visitors per year.
The Euro Space Center is an educational center dedicated to Space, which welcomes 15,000 young people per year, of 35 different nationalities, for 3 to 5 days of courses, as well as 70,000 visitors per year.


The Euro Space Center has an auditorium of 150 seats (including 4 seats for people with reduced mobility).
Its 30:10 screen offers a great flexibility for presentations, as does its Smart Board interactive screen. The recording option definitely makes this room a cutting-edge auditorium!
Cyberwal in Galaxia
Speakers
Cyberwal in Galaxia
Speakers
Tijl Atoui

Maxime Cordy

Xavier Devroye

Matteo Merialdo

Pascal Rogiest
President of the Scientific Committee
Our Program for the 5 days
The program includes theoretical & practical courses.
A break is scheduled every day in the morning and afternoon.
- Day 1
Monday 12/12
- Day 2
Tuesday 13/12
- Day 3
Wednesday 14/12
- Day 4
Thursday 15/12
- Day 5
Friday 16/12
9:30 AM – 10:30 AM
REGISTRATIONS
10:30 AM – 11:00 AM
- Auditorium
Luxembourg Seminar - 2nd Greater Region Software Engineering Research Days (SOFTER)
Each year, SOFTER brings together researchers from academia to discuss foundations, techniques, and tools for automating the analysis, design, implementation, testing, and maintenance of complex software systems. A special emphasis is put this year on Machine-Learning Systems.

Yves Le Traon - Full Professor in Computer Science - Systems and Software Reliability - Deputy Director of SnT
11:00 AM – 01:00 PM
- Auditorium
Research presentations
01:00 PM – 02:30 PM
LUNCH TIME
02:30 PM – 03:45 PM
- Auditorium
Panel on career progression

Axel Legay - Professor of Cyber Security - UCLouvain - President of the Scientific Committee
03:45 PM – 04:00 PM
COFFEE BREAK
04:00 PM – 06:00 PM
- Auditorium
Research presentations

Axel Legay - Professor of Cyber Security - UCLouvain - President of the Scientific Committee
02:30 PM – 04:15 PM
- ESEC (Redu)
Cyber Range technology and state of the art capabilities

Pascal Rogiest - Managing Director of the Cybersecurity Division of RHEA Group, Chief Strategy Officer of RHEA Group, Vice President of RHEA Belux

Matteo Merialdo - Deputy Director of the Operational Security Services Unit (ESEC - ESA) in Redu.
04:15 PM – 04:30 PM
COFFEE BREAK
04:30 PM – 06:00 PM
- ESEC (Redu)
CyberExcellence@ESEC
Building a State-of-the-Art Space Cyber Security Capacity
Be part of the game

Jean-Luc Trullemans - Head of the European Space Security and Education Centre (ESEC)
8:30 AM – 9:00 AM
REGISTRATIONS
9:00 AM – 9:30 AM
- Auditorium
Welcome to 2022 Cyberwal in Galaxia Program

Axel Legay - Professor of Cyber Security - UCLouvain - President of the Scientific Committee

Georges Cottin - Deputy General Manager of IDELUX
9:30 AM – 10:30 AM
- Auditorium
EU NIS2 Directive : enabler for more IT/OT security

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

Benoit Balliu - Howest Researcher in Industrial Security.
10:30 AM – 11:00 AM
- Auditorium
Introduction to OT/ICS Security

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

Benoit Balliu - Howest Researcher in Industrial Security.
11:00 AM – 12:30 PM
- Auditorium
Industrial Environment Scanning and Enumeration

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

Benoit Balliu - Howest Researcher in Industrial Security.
9:30 AM – 12:30 PM
- Auditorium
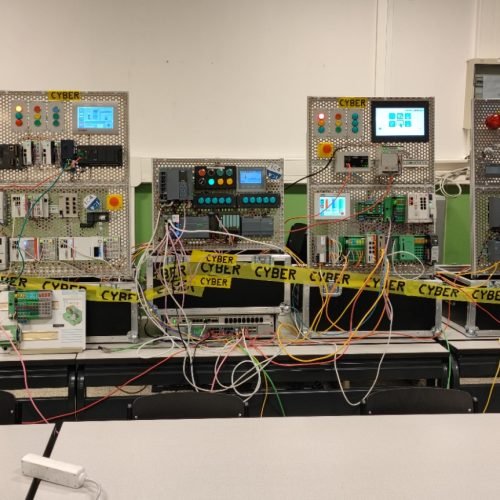
Theoretical part: Hands on - Industrial CTF on the Fictile Factor
Introduction to Industrial Control Systems
Basics of PLC Programming
Industrial Communication
Scanning ICS networks
Industrial Network & System enumeration
Reversing proprietary industrial protocols
Exploiting industrial control systems

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.
12:30 PM – 02:30 PM
LUNCH TIME
2:30 PM – 3:30 PM
- Freedom & ISS
Exploitation in an Industrial Environment
Fictile is a fast-growing fiction tile-producing company. Under the steady and continuous leadership of J.C. they are the unrivaled market leader in their sector since 2016. Their factory contains three halls. A hall with hydraulic presses, baking installation and a painting hall. To remain brand independent, the lead engineer of the factory decided to equip each hall with different types of industrial controllers. The three market leaders were chosen: Siemens, Beckhoff, and Phoenix Contact. According to investor K.C., there is no room in the budget for cyber-security. “Production must come first.”
Can you prove them wrong, by capturing all the flags?

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

Benoit Balliu - Howest Researcher in Industrial Security.
3:30 PM – 5:30 PM
- Freedom & ISS
Lab work: Hands on - Industrial CTF on the Fictile Factory

Kurt Callewaert - Howest Valorisation Manager Digital Transformation, Former Head of Research Applied Computer Science.

Tijl Atoui - Howest Cybersecurity Teacher and Researcher in Industrial Security and Fictile Factory maintaining

Benoit Balliu - Howest Researcher in Industrial Security.
6:00 PM – 8:00 PM
VIP Eurospace Center visit

- Moonwalk/Marswalk XP: Set your foot on the Moon and Mars
- Multi-axis chair: Test your reactions in a disorientation situation
- Space Flight Unit: Take control of your spaceship
- Free Fall Slide: Let yourself go into free fall
- Space Rotor: Feel the centrifugal force
- Mars Village: Get ready for life on Mars
In small groups, live a unique experience combining discovery and space simulations!
You will see demonstrations of 5 training simulators and discover the planet Mars as if you were there.
9:00 AM – 9:30 AM
REGISTRATIONS
09:30 AM – 10:45 AM
- Auditorium
Theoretical part: Malware Reverse Engineering
Software reverse engineering aims to analyse binary code, for which there is no corresponding source code available to the analyst, with a view to understand what it does and how it works. For malware analysis, it also aims to identify, defeat and eliminate the malware.
In this course, we introduce the four phases of reverse software engineering in the context of malware analysis:
- Basic static analysis reviews ways to get information from the structure of a binary executable. Important functionality and clues about the type of network communications used can be derived from the libraries the executable depends on.
- Basic dynamic analysis requires running the executable in an isolated or virtualised environment, in order to identify high level observable behaviour, such as modifications made to the system (e.g. created files, modified registry entries, etc) and network addresses the executable connects to, which can all be used to derive identification signatures.
- Advanced static analysis consists of analysing the actual instructions of the program, to gain a fine grained understanding of its operations.
This requires familiarity with assembly language constructs, which not only depend on the platform instruction-set, the operating system, but also the language and compiler used to create the executable.
- Advanced dynamic analysis is essentially binary debugging, used to examine the internal state of the running executable, giving not only a very detailed view of the operations of the executable, but also how it reacts to changes made to its internal state.
Laurent Mathy - Professor of Systems and Security in the Electrical Engineering and Computer Science.
10:45 AM – 11:00 AM
COFFEE BREAK
11:00 AM – 12:30 PM
- Auditorium
Theoretical part: Malware Reverse Engineering
Laurent Mathy - Professor of Systems and Security in the Electrical Engineering and Computer Science.
12:30 PM – 02:30 PM
LUNCH TIME
02:30 PM – 04:00 PM
- Freedom & ISS
Lab work: Malware Reverse Engineering
For these topics, after a theoretical review, we also present some anti-analysis techniques used in malware to prevent or hinder analysis, as well as labs to illustrate and put the acquired knowledge into practice.
Laurent Mathy - Professor of Systems and Security in the Electrical Engineering and Computer Science.
04:00 PM – 04:15 PM
COFFEE BREAK
04:15 PM – 05:30 PM
- Freedom & ISS
Lab work: Malware Reverse Engineering
Laurent Mathy - Professor of Systems and Security in the Electrical Engineering and Computer Science.
06:30 PM – 07:30 PM
- Hub
Aperitif
07:30 PM – 10:30 PM
- Voyager Café
Gala Dinner at the Euro Space Center
On this day, students have the opportunity to choose between two courses, one on testing which starts at 9:30 am and the other on Federated Learning which starts at 10:30 am. The syllabus of both courses is given below.
9:00 AM – 9:30 AM
REGISTRATIONS
09:30 AM – 12:30 PM
- Freedom & ISS
Theoretical part: Certification oriented cybersecurity testing of cyber physical systems with fuzzing techniques
The course aims to teach students how to use fuzzing techniques for cybersecurity testing of cyber physical systems. The course introduces relevant cybersecurity certification schemes and explains how to design the testing process for certification evidence gathering.
The course is composed of three parts: 1) cybersecurity certification and testing, 2) cybersecurity testing processes, and 3) Dynamic testing and fuzzing techniques.
The course starts by providing an overview of product and process cybersecurity schemes and introducing the NIS directive with it’s focus on risk analysis.
The course then describes the requirements that certification schemes impose on the testing process such as maintaining traceability between risk analysis and testing.
The course then introduces the Common Criteria product certification scheme and its concepts of protection profile and evaluation assurance level that will be used in the practical work.
The second part of the course then provides an overview of the different phases of the penetration testing process and the tools that can be used during each phase.
The third part of the course focuses on dynamic testing fuzzing techniques and how to use them to test cyber physical systems. The general fuzzing process is then introduced along with a description of black-box, white-box and grey box-fuzzing. The state of the art in fuzzing is then presented with an overview of fuzzing tools.

Xavier Devroye - Assistant Professor of Software Engineering at the Namur Digital Institute and the Faculty of Computer Science of the University of Namur.

Christophe Ponsard - Research-Innovation-Exploitation Coordinator.
10:30 AM – 12:30 PM
- Freedom & ISS
Theoretical part: Secure Federated Learning
The course aims to introduce students to the understanding of different Federated Learning concepts with a focus on security vulnerabilities and cyber security challenges. The course will introduce the Federated Learning and compare it to other Machine Learning approaches.
The main concepts and process of Federated Learning will then be presented. The model aggregation phase will then be presented along with the security threats. The concept of differential privacy and its relevance for federated Learning explained. Homomorphic encryption techniques will then be introduced for securing the federated Learning process.
The course will then present open-source frameworks for federated learning that will be used in the practical work.

Xavier Lessage - Senior Research Engineer in the Data Science department at CETIC.
12:30 PM – 02:30 PM
LUNCH TIME
02:30 PM – 05:30 PM
- Freedom & ISS
Lab work: Certification oriented cybersecurity testing of cyber physical systems with fuzzing techniques
The practical work will apply the certification and fuzzing concepts presented in the course to a mobility case study composed of virtualized rovers that navigate on the road under the supervision of a traffic control system. The rover software and firmware needs to be updated on a regular basis. The practical work will involve performing an impact analysis to determine if certified components are impacted, performing fuzzing tests to detect possible vulnerabilities and reporting on the tests required by the impact analysis.

Xavier Devroye - Assistant Professor of Software Engineering at the Namur Digital Institute and the Faculty of Computer Science of the University of Namur.

Guillaume Ginis - Senior Researcher in Cybersecurity at CETIC.
02:30 PM – 04:30 PM
- Freedom & ISS
Lab work: Secure Federated Learning
The practical work aims at applying Federated Learning concepts with a practical exercise from the medical/hospital domain (classification of medical images (malignant or benign lesions)). The practical work will cover the steps required to train a neural network (CNN) with a Federated learning architecture. The practical work will involve adapting the model to meet cybersecurity challenges and performing cybersecurity tests.

Xavier Lessage - Senior Research Engineer in the Data Science department at CETIC.
8:00 AM – 8:30 AM
REGISTRATIONS
8:30 AM – 10:00 AM
- Auditorium
Theoretical part: Machine Learning Security in the Real World
Adversarial attacks are considered as one of the most critical security threats for Machine Learning (ML). These attacks apply small perturbations to some original examples in order to produce adversarial examples, specifically designed to fool ML model decision.
In order to enable the secure deployment of ML models in the real world, it is essential to properly assess their robustness to adversarial attacks and develop means to make models more robust. A common way to assess robustness is to empirically compute the model performance on the adversarial examples that an attack produced from a set of original examples.
Similarly, the established way to harden ML models is adversarial hardening, i.e. training processes that make models learn to make correct predictions on adversarial examples.
Traditional adversarial attacks were designed for image recognition and assume that every image pixel can be modified independently to its full range of values. In many domains, however, these attacks fail to consider that only specific perturbations could occur in practice due to the hard domain constraints that delimit the set of valid inputs (e.g., financial transactions must have a positive amount, text must be linguistically consistent, medical images can change depending on the machine used and patients’ morphology, etc.).
Because of this, they almost-always produce examples that are not feasible (i.e. could not exist in the real world).
As a result, research has developed real-world adversarial attacks that either manipulate real objects through a series of problem-space transformations (i.e. problem-space attacks) or generate feature perturbations that satisfy predefined domain constraints (i.e. constrained feature space attacks).
In this lecture, we will review the scientific literature on these attacks and report on our experience in applying them to real-world cases.

Maxime Cordy - Research Scientist at the Interdisciplinary Center for Security, Reliability and Trust (SnT)
10:00 AM – 12:00 PM
- Freedom & ISS
Lab work: Machine Learning Security in the Real World
During the lab, the students will gain practical knowledge on adversarial attacks via an online game and a hands-on exercise.

Maxime Cordy - Research Scientist at the Interdisciplinary Center for Security, Reliability and Trust (SnT)
The next editions of Cyberwal in Galaxia Program are already planned for 2023 and 2024.
The next editions of Cyberwal in Galaxia Program are already planned for 2023 and 2024.
Register now!
2022 Cyberwal in Galaxia . .. ...
Registration
Register now to be a part of this exclusive event!
End of registrations on 05/12
*Your registration includes:
- Courses & practical work
- Shuttle bus from the hotel to Galaxia
- Meals (lunch & coffee breaks)
- VIP visit to Euro Space Center
- Gala dinner
Not included:
- Hotel
- Breakfast
- Evening meals
Hotels
Join us for the Cyberwal in Galaxia Program second edition and enjoy an exclusive room rate at Mecure Hotel, including breakfast! Book now, limited rooms available at this special rate!
The availability and preferential price are not guaranteed after 12/11.

Journey
Gala dinner
Meat & fish meal
Tartare de St Jacques, quinoa et légumes racines crème acidulée, jet de pois gourmand
Vin: Domaine Boucabeille « Les Terrasses » Blanc
***
Carré de veau braisé, jus au thym et romarin croquant de ris et carottes fondantes plate de Florenville à la fleur de sel
Vin: Château la Roc de Calon Bordeau Rouge
***
Gros macarons vanille mascarpone et spéculoos
Fish meal
Tartare de St Jacques, quinoa et légumes racines crème acidulée, jet de pois gourmand
Vin: Viré Clessé Blanc
* * *
Dos de Cabillaud roti Risotto de légumes verts et bouillon de coquillage
Vin: Château la Croix de Guillot Rouge
* * *
Gros macarons vanille mascarpone et spéculoos
Vegan meal
Tartare de choux-fleurs, quinoa et légumes racines vinaigrette de légumes et jet de pois gourmand
Vin : Viré Clessé Blanc
* * *
Risotto de légumes verts
Feuille de riz craquante et bouillon d’herbes
Vin : Château la Croix de Guillot Rouge
* * *
Tartare de mangue et sorbet pomme
OUR BEST PARTNERS
This Program, which is financed by the Walloon Region, is organized by IDELUX Development (the Economic Development Agency of Belgian Luxembourg) and under the authority of the scientific committee chaired by Mr Axel Legay, Professor of cybersecurity at the UC Louvain.